The proliferation of API-driven architectures for insurance firms has fundamentally transformed how carriers exchange data with partners, integrate insuretech solutions, and deliver digital experiences to customers. As insurance organizations accelerate their digital transformation initiatives, establishing comprehensive API security best practices has become a strategic imperative—not merely a technical consideration, but a foundational requirement for operational resilience, regulatory compliance, and competitive differentiation.
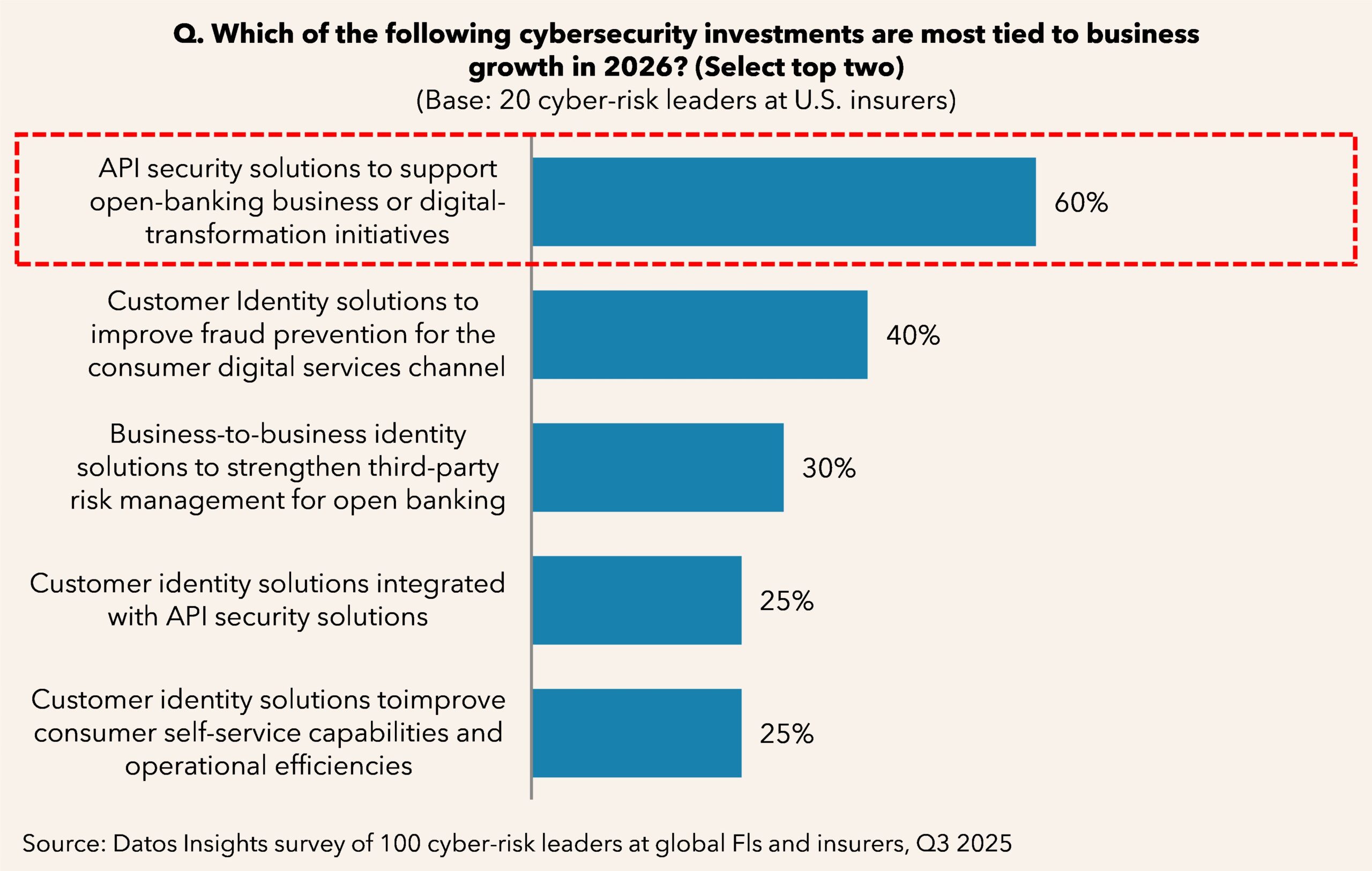
This report examines the critical intersection of API security and carrier digital transformation, providing insurance executives, CISOs, and technology leaders with actionable frameworks for managing API security risks across complex partner ecosystems. It is based on personal interviews with CISOs of insurance companies and insuretech vendors and a selection of relevant survey results from Datos Insights’ Q3 2025 survey of 20 insurance carrier buyers.
Clients of Datos Insights’ Cybersecurity service can download this report.
This report mentions the NAIC, the Association for Cooperative Operations Research and Development (ACORD), the Insured Retirement Institute (IRI), B3i Services AG (B3i), and LIMRA.
About the Author

Jane Ginn
Jane Ginn is a cybersecurity analyst with extensive knowledge of the cybersecurity industry and cyber threat intelligence tradecraft. She is a leader and manager with over 35 years of experience in information technology, international business, and engineering consulting. From 2014 to 2023, she served as the Secretary of the Organization for the Advancement of Structured Information Systems (OASIS) Cyber Threat...
Other Authors

John Horn
John Horn leads the Cybersecurity practice at Datos Insights, which provides valuable cybersecurity and identity research, insights, and advisory services to financial services firms. In addition to leading a team of Strategic Advisors, John functions as a distinguished industry expert and critical thinker within the rapidly evolving domains of identity, cybersecurity, and risk. His coverage areas include identity security, identity and access...
