Boston, April 4, 2019 – When a financial institution’s mobile app can be decompiled, adversaries can access sensitive information inside the source code, which may lead to a range of exploits against the FI or its customers. And there is no shortage of evidence that hackers are actively seeking to leverage those vulnerabilities. Application shielding as well as threat detection and response can strengthen the security of mobile apps, but if financial services companies fail to apply these technologies to their apps, they leave a monumental attack surface exposed.
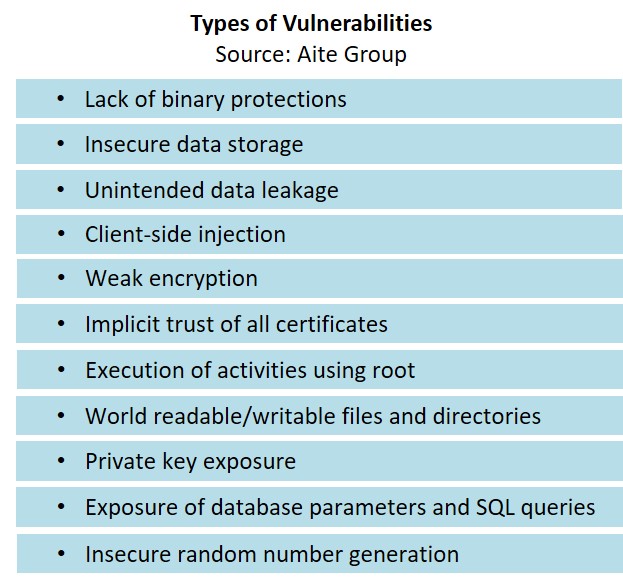
This report is sponsored by Arxan and analyzes the perceived security of FIs’ mobile apps across every vertical in financial services. To conduct this research, Aite Group decompiled the mobile applications of 30 FIs over a six-week period, and the report details the specific vulnerabilities and consequences, accentuating the prodigious size of this problem.
This 21-page Impact Report contains eight figures and three tables. Clients of Aite Group’s Cybersecurity service can download this report, the corresponding charts, and the Executive Impact Deck.
This report mentions [24]7.ai, Aptoide, Buffer, Google, the Internal Revenue Service, Instagram, McDonald’s, Microsoft, Panera Bread, PayPal, PortSwigger, Rakuten, Salesforce, Facebook, Snap, T-Mobile, TutuApp, TweakBox, Twitter, and WhatsApp.
About the Author
Datos Insights
We are the advisor of choice to the banking, insurance, securities, and retail technology industries–both the financial institutions and the technology providers who serve them. The Datos Insights mission is to help our clients make better technology decisions so they can protect and grow their customers’ assets.